RPG
Protect your valuable data!
Cryptographically random memorable passwords…
An endless variety awaits. No guessable connection to you, easier to remember and type!
- Words make longer passwords as easy as short passwords!
- Pronounceable scrambled passwords!
- Completely random passwords!
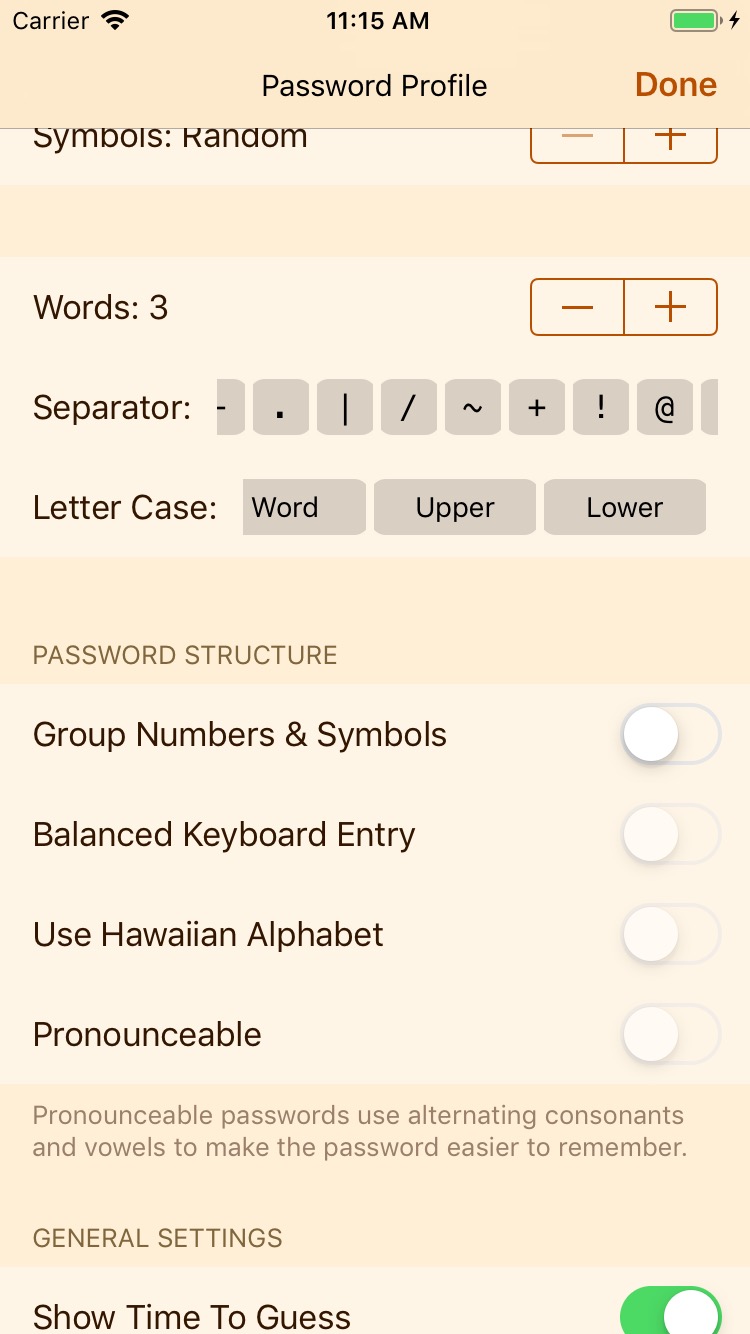
Passwords Tailored For You
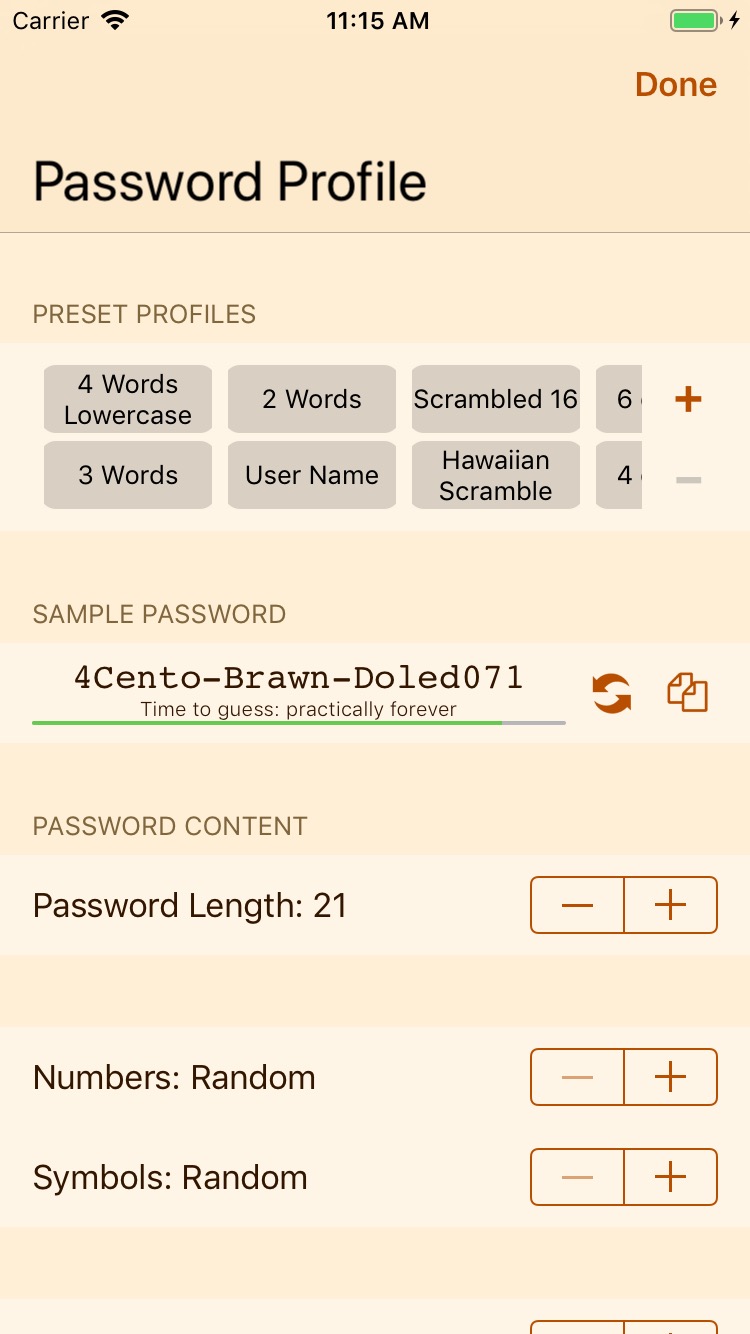
Choose a password formula that works for you!
- Mix words with as many symbols and numbers as you like
- Balanced keyboard and pronounceable make scrambled passwords better!
- Keep the symbols and numbers together for easier passwords!
all_inclusive
Many combinations!
Choose the balance of words, letters, numbers, and symbols that meets your needs.
account_balance
Financial Security!
Create new PINs for your credit cards, passwords for your bank accounts!
email
Email Protection!
Your email account is critical. Keep it secure!
folder
Passwords for any purpose!
Protect your data!
verified_user
Protect your online identity!
Strong Passwords for your Online Services
Strong Passwords: More Important Than Ever.
Your birthday is not a good password.
Don’t let your bank account or your email get hacked.
Change your password regularly, and use a random password to keep attackers guessing.
Password Features
RPG provides:
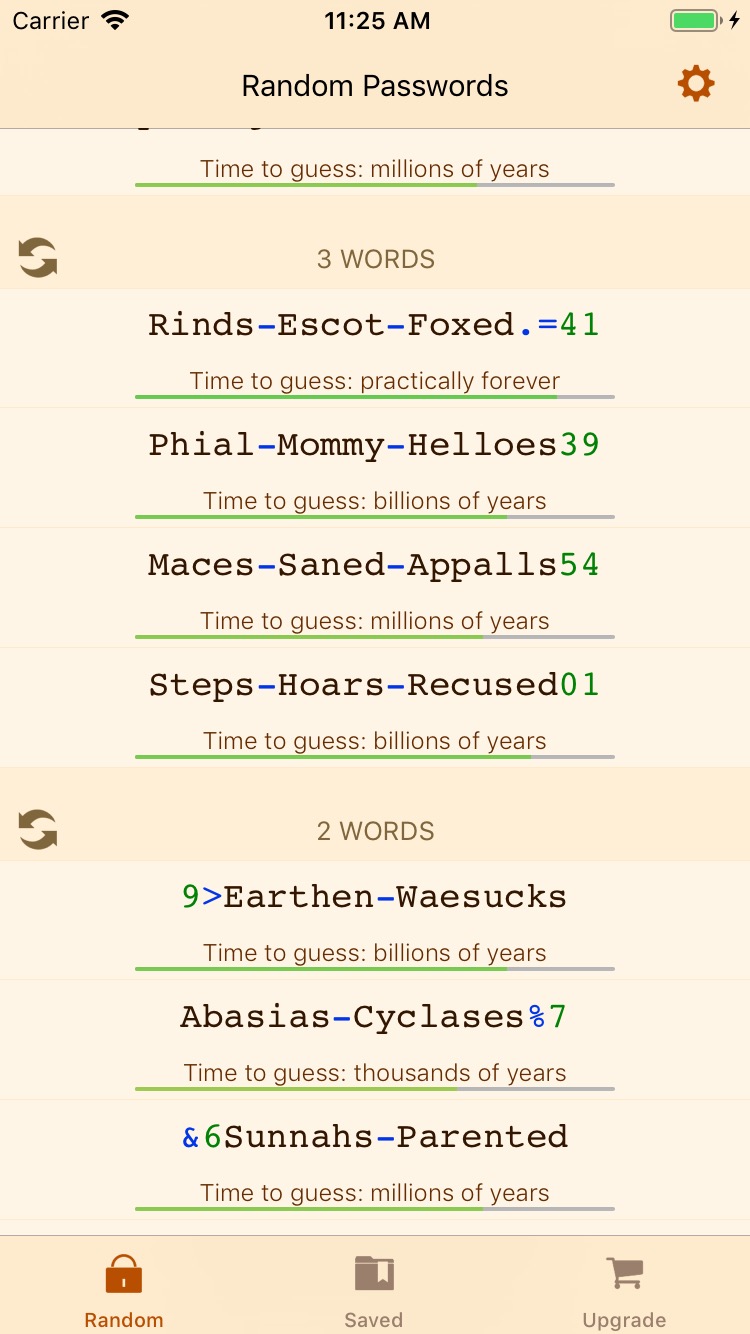
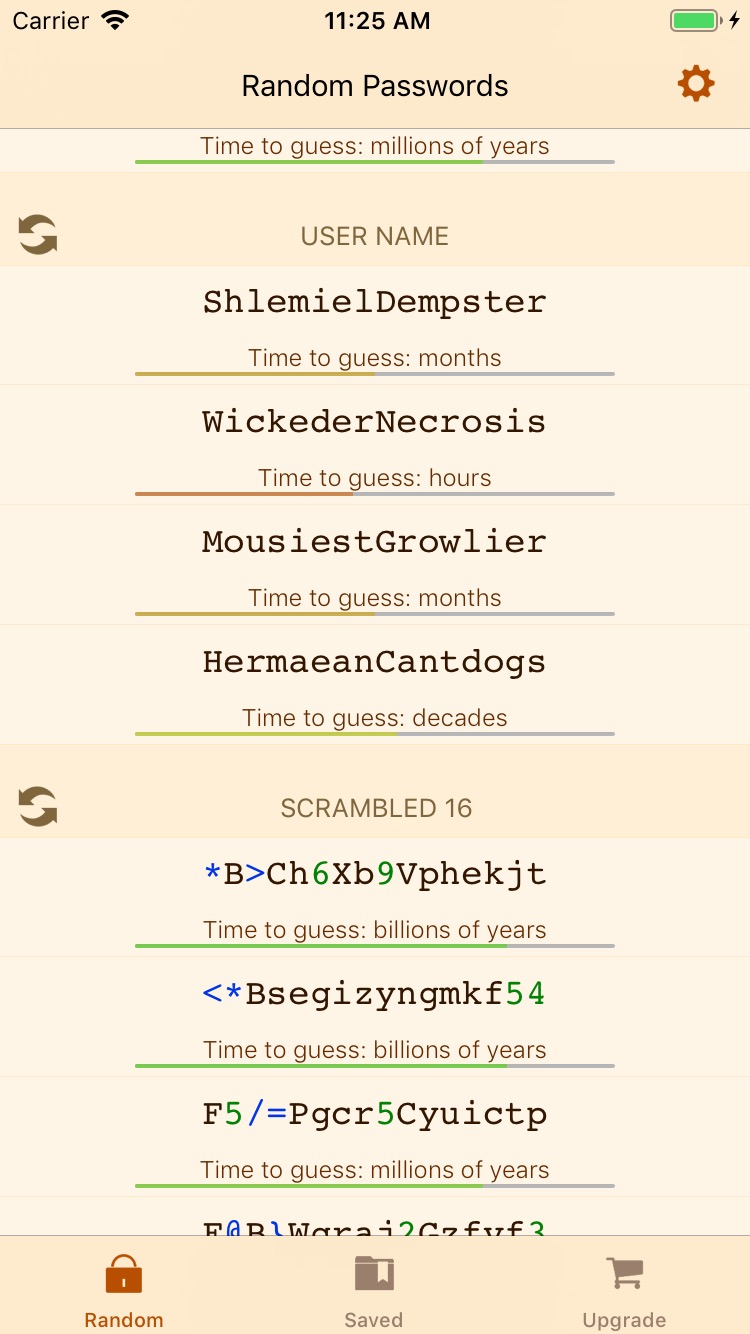
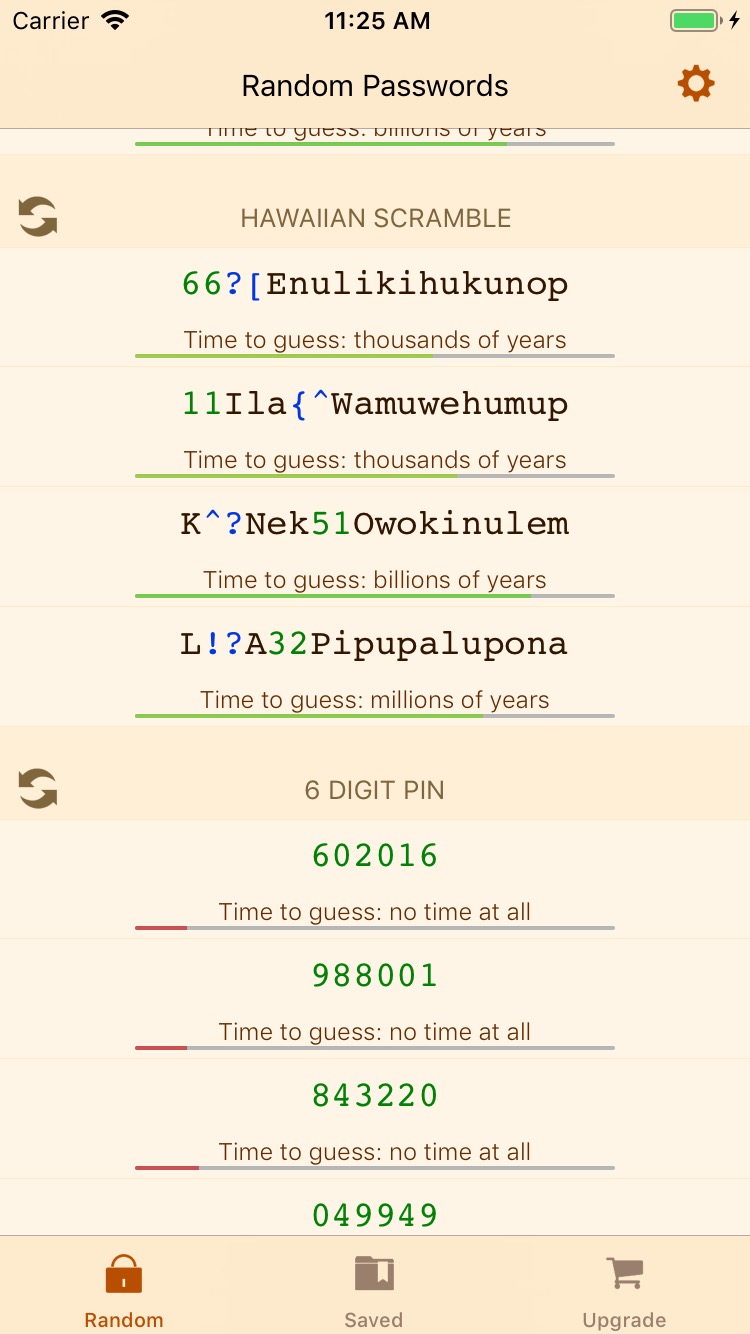
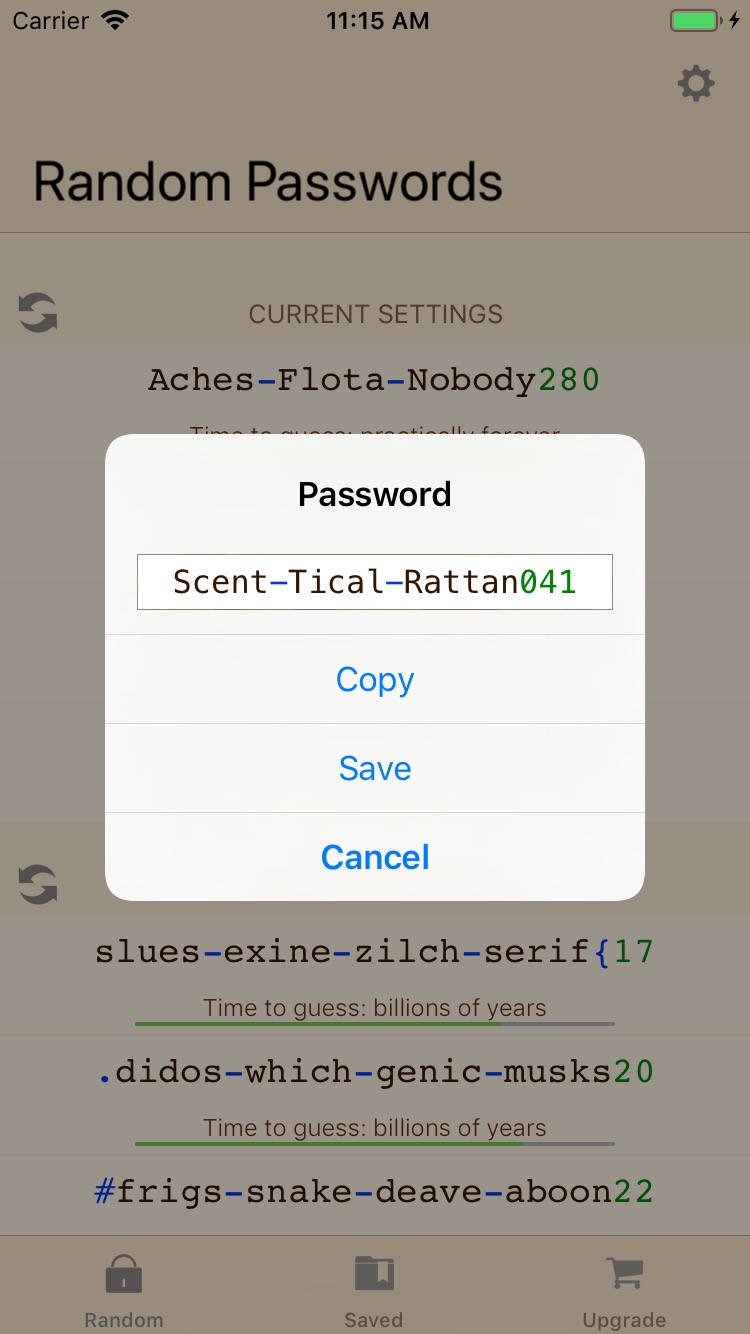
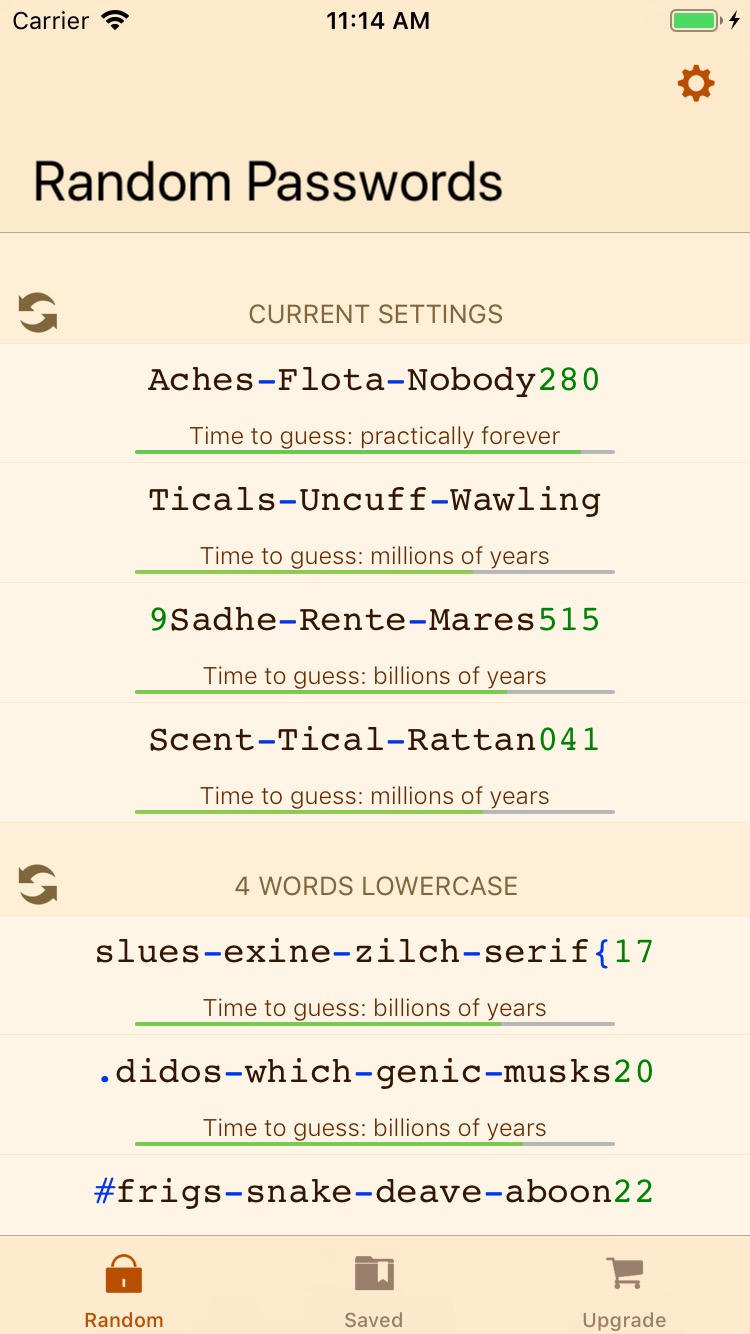
- Cryptographically random passwords that include typically required combinations of letters, numbers, and symbols. Passwords are color-coded according to their strength.
- Word-based Passwords using multiple words to fill out the length and complexity requirements. Words make passwords easier to remember and they can provide nearly the same level of security if you mix symbols and numbers in and keep them long.
- Memorable scrambled passwords constructed of the same characters but arranged so that vowels and consonants are kept away from each other. This usually helps the random passwords to be pronounceable as if they were words.
- Hawaiian scrambled passwords using the smaller Hawaiian alphabet instead of the regular English alphabet for Memorable passwords. This gives the passwords a fun tropical feeling. It technically reduces the password complexity but only if the attacker knows you used a Hawaiian password.
- Balanced scrambled passwords: By alternating letters on the left and right sides of the keyboard, balanced passwords can be typed very quickly.
- Password Complexity Estimates: RPG provides the approximate amount of time required to guess each password.
- Several password options at once: You never know who might be watching. Choose your password and memorize it without touching your screen.
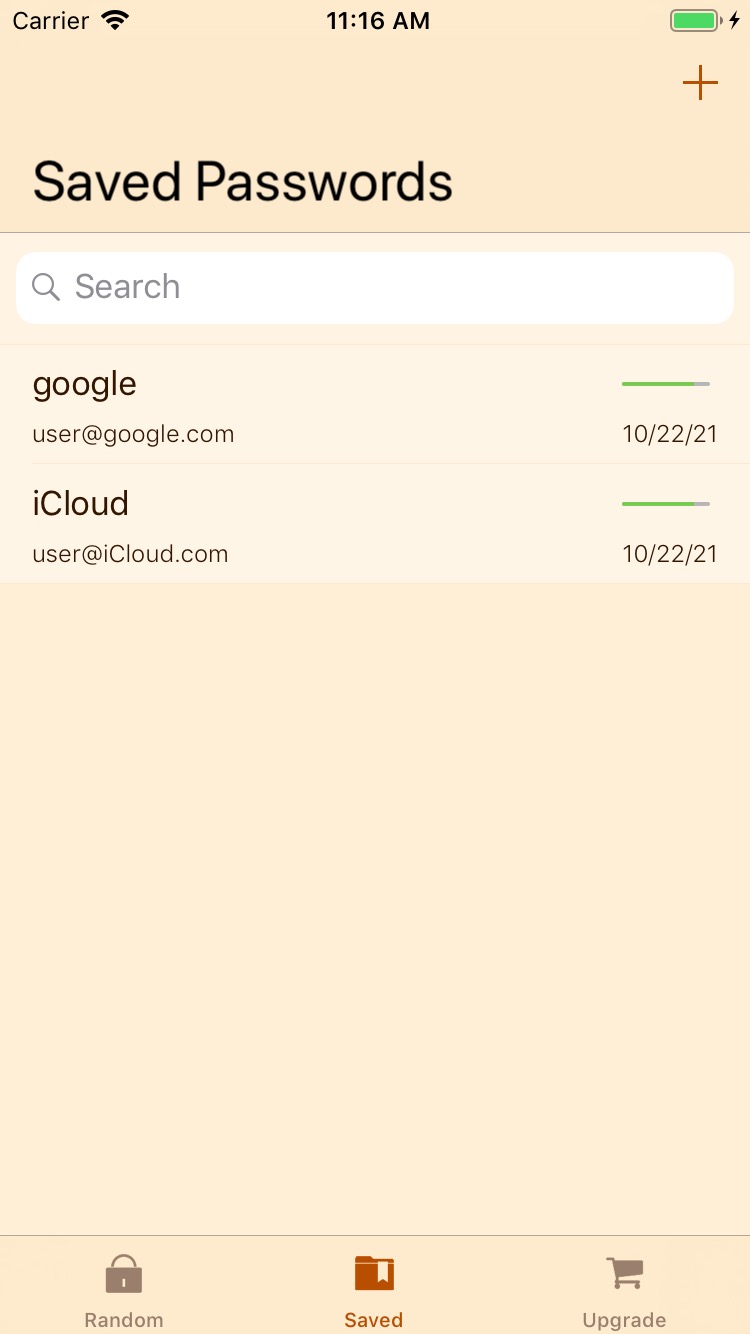
- Secure storage in your iCloud keychain Save and retrieve your passwords right in RPG. Passwords are synchronized securely with your other iCloud devices. RPG works as a credential provider too - you can retrieve your saved password securely on your iOS device just when you need it; no copy/paste required!
- Password age You should change your passwords periodically. RPG keeps track of when you last updated each saved password so you know which ones are getting stale.
How Secure Passwords Work
Many techniques used to get past password schemes are rendered ineffective by randomly generated passwords like these.
- Attackers look for the easiest approach to crack your password.
- With the “Dictionary” approach, the attacker uses a list or dictionary of passwords to guess. This includes password lists stolen from websites, lists of names, places, and all known words in a given language.
- With the “Brute Force” approach, the attacker tries every possible character in every possible position up to the maximum password length accepted by the system being attacked.
- Dictionary words alone are easily compromised. The English language contains roughly 200,000 words. A password cracking system capable of 500 billion guesses per second could process the entire English language dictionary, along with all common names and nicknames and dates, within a second or less. While easy to remember, dictionary words alone offer little protection because the attacker needs relatively few tries using standard dictionaries to guess the password.
- Cryptographically Random passwords are generated using random number algorithms suitable for cryptographic operations because they do not repeat. Repeating sequences would make the application into its own decoder ring.
- Entropy is a measure of password complexity, relating to the sheer number of permutations of the available password characters for a given length.
- RPG translates Entropy into a convenient time estimate, assuming a password cracking machine capable of making 500 billion guesses per second.
- A 7 letter password containing uppercase, lowercase, numbers, and punctuation has an entropy value of 45, and at 500 billion guesses per second, such a password could guessed in a matter of seconds.
- A longer password with 8 characters has an entropy value of 51 and would require hours to guess.
- A 15 character password with an entropy of 96 would require billions of years to guess.
- Pass phrases make things more difficult for the attacker who needs to try all possible combinations of dictionary words. Mix in a few numbers and symbols, and the attacker is left with the brute-force strategy. Keep the total length over 16 characters, and the attacker is faced with a daunting challenge.
Using Secure Passwords
Some things to remember about passwords:
- Longer passwords, with more kinds of characters in the password provides better protection. Use a mixture of uppercase, lowercase, numbers, and symbols.
- Use a different password for every on-line account you have, so that if one is compromised the rest are still safe.
- Use the same rules for user IDs: Use a password from this app as your user ID! Web sites often store the user ID unencrypted, so personally identifiable user IDs make it easier for a hacker to target your account if a web site’s password scheme is compromised.
- Don’t keep a list of your hard-to-remember passwords on your computer. It can be easier for hackers to steal data on your computer than it is for them to steal data on a sheet of paper in your wallet or in your home. Store them on paper someplace safe.
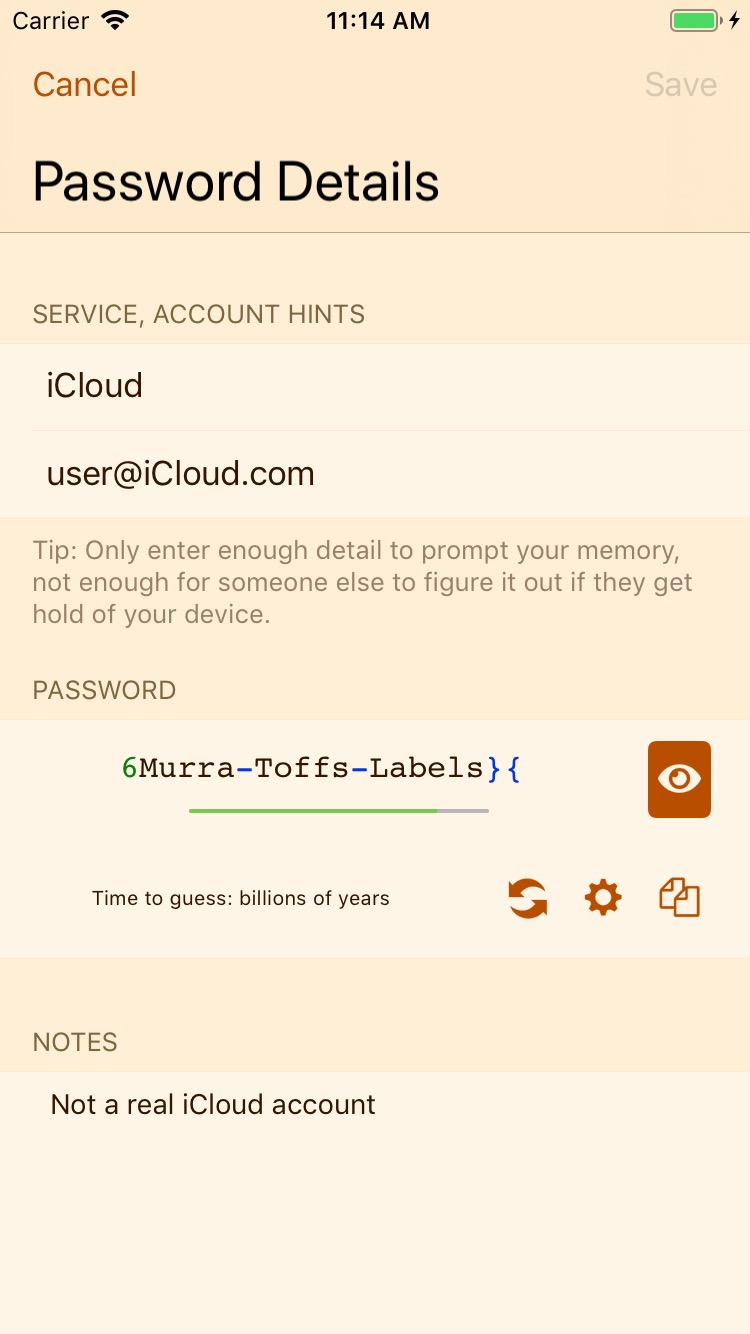
- Don’t store the key next to the lock: Wherever you choose to manage your passwords, use as little information as possible to remind you what the password is for. Invent a coding scheme for web sites and user names. If someone recovers your password list, make it harder for them to figure out the web site and user name you use with the password.
- Move the uppercase letters around: The app capitalizes passwords to make them easier to read, but you can edit the password before copying it and capitalize one or more of the other letters in each word.
You can learn more about password strength here.